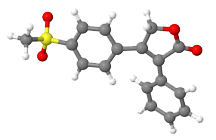
A model of the chemical structure of Rofecoxib, the active ingredient of Vioxx. At a U.S. Senate Finance Committee hearing on November 18, 2004, Dr. David Graham, a safety scientist for the U.S. Food and Drug Administration, testified that the agency's handling of Merck & Co Inc.'s withdrawn painkiller Vioxx, was a "profound regulatory failure" by an agency "incapable of protecting America" from another dangerous drug. Shortly thereafter, as reported by Marc Kaufman in The Washington Post, the nonprofit Government Accountability Project (GAP), which assists whistleblowers, started receiving anonymous telephone calls discrediting Dr. Graham and his work. With a little sleuthing, the GAP staff members were able to determine that the calls were coming from Dr. Graham's FDA managers. This incident is an example of a professional attack that failed. Many succeed. Image (CC by SA 3.0) by Tarique012.
If you work in an organization that has transgressed in a serious way, you might be considering whether or not to make information available to the public, the media, or to government authorities. If you continue to work there, and you have knowledge of violations, you might be involving yourself in illegal behavior, or at the very least, violating your own moral code. Sorting through these questions is much easier if you have professional support from an attorney, a counselor, or a therapist.
As difficult as these issues are, there are other matters to consider. Specifically, if you do "blow the whistle," how will your employer respond? How will your fellow employees respond?
There are obvious responses, including denials, personal attacks, reassignment, harassment, vandalism, termination, blackmail, extortion, and even brutality. Famous cases of whistleblowers are littered with these obvious measures. Here's Part I of a little catalog of some less-obvious tactics for which it's more difficult to prepare oneself.
- Other whistleblowers
- People in these situations tend not to consider the possibility that someone else has already blown the whistle, or is about to. If that happens to you, then you might already have been targeted for investigation; you might already be regarded as a co-conspirator.
- Perform an inventory of people you know who have information that could incriminate you. Assess the likelihood that someone is already conferring with authorities. If you sense that you're vulnerable, seek counsel and act quickly. If you think you still have some time, estimate how much time you have and get busy preparing material to use if you do contact authorities. Even if you act too late, a freshly prepared store of material could lend credibility to your claim that you were intending to act.
- Professional attacks
- If the whistleblowerProspective whistleblowers tend not
to consider the possibility that
someone else has already blown
the whistle, or is about to or prospective whistleblower is in a technical or specialized job, questions about the work products of the whistleblower are generally technical. For this reason, direct professional attacks of the obvious type might be effective, but evaluating them is difficult for people outside the profession. A more effective family of tactics involves degrading the whistleblower's own work products, so as to cause colleagues to discredit the whistleblower professionally. Direct tampering is possible, but so is tampering with data, devices, or the quality of materials upon which the whistleblower's own work depends. - If you suddenly detect irregularities in your own work products, or in the resources on which your work products depend, reporting them through formal, regular channels might not be wise, because it signals the tamperers that you're aware of what they've done. Instead, consider enhancing security protecting your work, or creating a duplicate and far more secure version of your work, while allowing the tamperers to continue their operations on a false, less-secure version.
We'll continue next time, exploring more tactics that can erode whistleblower credibility. Next in this series ![]() Top
Top ![]() Next Issue
Next Issue
Is every other day a tense, anxious, angry misery as you watch people around you, who couldn't even think their way through a game of Jacks, win at workplace politics and steal the credit and glory for just about everyone's best work including yours? Read 303 Secrets of Workplace Politics, filled with tips and techniques for succeeding in workplace politics. More info
Your comments are welcome
Would you like to see your comments posted here? rbrendPtoGuFOkTSMQOzxner@ChacEgGqaylUnkmwIkkwoCanyon.comSend me your comments by email, or by Web form.About Point Lookout
 Thank you for reading this article. I hope you enjoyed it and
found it useful, and that you'll consider recommending it to a friend.
Thank you for reading this article. I hope you enjoyed it and
found it useful, and that you'll consider recommending it to a friend.
This article in its entirety was written by a human being. No machine intelligence was involved in any way.
Point Lookout is a free weekly email newsletter. Browse the archive of past issues. Subscribe for free.
Support Point Lookout by joining the Friends of Point Lookout, as an individual or as an organization.
Do you face a complex interpersonal situation? Send it in, anonymously if you like, and I'll give you my two cents.
Related articles
More articles on Workplace Politics:
 What Do You Need?
What Do You Need?- When working issues jointly with others, especially with one other, we sometimes hear, "What do
you need to make this work?" Your answers can doom your effort — or make it a smashing success.
 Social Transactions: We're Doing It My Way
Social Transactions: We're Doing It My Way- We have choices about how we conduct social transactions — greetings, partings, opening doors,
and so on. Some transactions require that we collaborate with others. In social transactions, how do
we decide whose preferences rule?
 Embarrassment, Shame, and Guilt at Work: Creation
Embarrassment, Shame, and Guilt at Work: Creation- Three feelings are often confused with each other: embarrassment, shame, and guilt. To understand how
to cope with these feelings, begin by understanding what different kinds of situations we use when we
create these feelings.
 I Don't Understand: I
I Don't Understand: I- When someone makes a statement or offers an explanation that's unclear or ambiguous, there are risks
associated with asking for clarification. The risks can seem so terrifying that we decide not to ask.
What keeps us from seeking clarification?
 Time to Let Go of Plan A
Time to Let Go of Plan A- We had a plan. It was a good one. Our plan seemed to work for a while. But then troubles began. And
now things look very bleak. But people can't let go of the plan. For some teams in this situation, there
isn't a Plan B. For others, Plan B is a secret.
See also Workplace Politics and Managing Your Boss for more related articles.
Forthcoming issues of Point Lookout
 Coming April 24: Antipatterns for Time-Constrained Communication: 1
Coming April 24: Antipatterns for Time-Constrained Communication: 1- Knowing how to recognize just a few patterns that can lead to miscommunication can be helpful in reducing the incidence of problems. Here is Part 1 of a collection of communication antipatterns that arise in technical communication under time pressure. Available here and by RSS on April 24.
 And on May 1: Antipatterns for Time-Constrained Communication: 2
And on May 1: Antipatterns for Time-Constrained Communication: 2- Recognizing just a few patterns that can lead to miscommunication can reduce the incidence of problems. Here is Part 2 of a collection of antipatterns that arise in technical communication under time pressure, emphasizing those that depend on content. Available here and by RSS on May 1.
Coaching services
I offer email and telephone coaching at both corporate and individual rates. Contact Rick for details at rbrendPtoGuFOkTSMQOzxner@ChacEgGqaylUnkmwIkkwoCanyon.com or (650) 787-6475, or toll-free in the continental US at (866) 378-5470.
Get the ebook!
Past issues of Point Lookout are available in six ebooks:
- Get 2001-2 in Geese Don't Land on Twigs (PDF, )
- Get 2003-4 in Why Dogs Wag (PDF, )
- Get 2005-6 in Loopy Things We Do (PDF, )
- Get 2007-8 in Things We Believe That Maybe Aren't So True (PDF, )
- Get 2009-10 in The Questions Not Asked (PDF, )
- Get all of the first twelve years (2001-2012) in The Collected Issues of Point Lookout (PDF, )
Are you a writer, editor or publisher on deadline? Are you looking for an article that will get people talking and get compliments flying your way? You can have 500-1000 words in your inbox in one hour. License any article from this Web site. More info
Follow Rick
Recommend this issue to a friend
Send an email message to a friend
rbrendPtoGuFOkTSMQOzxner@ChacEgGqaylUnkmwIkkwoCanyon.comSend a message to Rick
![]() A Tip A Day feed
A Tip A Day feed
![]() Point Lookout weekly feed
Point Lookout weekly feed
 My blog, Technical Debt for Policymakers, offers
resources, insights, and conversations of interest to policymakers who are concerned with managing
technical debt within their organizations. Get the millstone of technical debt off the neck of your
organization!
My blog, Technical Debt for Policymakers, offers
resources, insights, and conversations of interest to policymakers who are concerned with managing
technical debt within their organizations. Get the millstone of technical debt off the neck of your
organization!Beware any resource that speaks of "winning" at workplace politics or "defeating" it. You can benefit or not, but there is no score-keeping, and it isn't a game.
- Wikipedia has a nice article with a list of additional resources
- Some public libraries offer collections. Here's an example from Saskatoon.
- Check my own links collection
- LinkedIn's Office Politics discussion group
