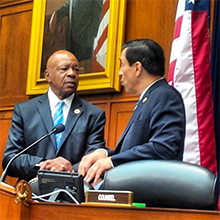
Rep. Darryl Issa (right), Chairman of the Oversight and Government Reform Committee of the U.S. House of Representatives of the 112th and 113th U.S. Congresses, and Rep. Elijah Cummings (left), Ranking Member of the committee. On March 5, 2014, during a hearing being conducted by the committee, Chairman Issa interrupted the testimony of Ms. Lois Lerner, former Director of the Exempt Organizations Unit of the U.S. Internal Revenue Service, and after a brief explanation, adjourned the hearing. Ms. Lerner had been in the midst of being questioned, and on advice of counsel, she had been responding to all questions by invoking her Fifth Amendment right not to testify because her testimony might tend to incriminate her. After a number of such responses, Chairman Issa apparently lost control of himself, unable to withstand Ms. Lerner's persistent invocation of Fifth Amendment rights. By abruptly terminating the hearing, over Rep. Cummings' forceful protestations, and even cutting off Rep. Cummings' microphone, Chairman Issa violated committee rules and customs of long standing. He thereby created an arguably bitter confrontation, which ultimately led to his public apology to Rep. Cummings. Watch the entire incident. Photo courtesy U.S. House of Representatives.
We're all flawed. We don't always behave in the way we hoped we would. Sometimes, our errors are 100% our own doing. And sometimes, what we regret is our response to what someone else has said or done (or hasn't said or hasn't done), intending to cause us to slip. We have names for that kind of error. We call it "taking the bait," "falling for that trap," "caving under pressure," or other similar phrases.
Successfully avoiding such traps is described as "showing grace under fire," "keeping your cool," or "keeping your head." Searching for tips about how to do that, we find suggestions like "control your emotions," "be positive," or "don't take it personally." But how does one do that?
Recognizing attackers' tactics in the moment, as they're being used, is helpful. Some tactics are obvious to most people, but here's a little catalog of some of the less obvious tactics people use to bait others.
- Cloaked insults
- Cloaked insults accomplish the attacker's goal more effectively than do obvious insults, because, to witnesses, a graceless response to obvious insults is understandable. But a comment that's insulting only if one knows important information might instead seem to be an innocent, factual observation. Responding gracelessly to such comments can seem to be over the top or inexplicable. Examples of cloaked insults include references to past private disagreements, or oblique references to the target's past failures or transgressions.
- Subtle attacks
- When attacks are subtle enough, they don't appear to bystanders to be attacks at all. As an example of a subtle attack, consider an assertion that the attacker expects to be selected for a possible future assignment to which both attacker and target aspire, but which bystander witnesses know little about. Witnesses might see the remark as innocent; the target might see it otherwise. Counterattacking, even deftly, can seem to be unprovoked.
- Verbal triggering
- If attacker When attacks are subtle enough,
they don't appear to bystanders
to be attacks at alland target have had a relationship of significant duration, or if somehow the attacker has gained knowledge of topics that are sore spots for the target, the attacker can use word choices that bring these tender areas to mind for the target. For example, consider a discussion at a meeting. If the target led an effort in the past that is now widely regarded as a disappointment, the attacker can use an example from that effort as an illustration in support of a point someone else has made in the course of the current discussion. The attacker thus makes it necessary for the target to expend effort to maintain composure. In itself, this barb might not precipitate the target's loss of composure, but such expenditures of effort do accumulate. See "Ego Depletion: An Introduction," Point Lookout for November 20, 2013 for more.
We'll continue next time with more techniques for baiting other people. Next in this series ![]() Top
Top ![]() Next Issue
Next Issue
Are you fed up with tense, explosive meetings? Are you or a colleague the target of a bully? Destructive conflict can ruin organizations. But if we believe that all conflict is destructive, and that we can somehow eliminate conflict, or that conflict is an enemy of productivity, then we're in conflict with Conflict itself. Read 101 Tips for Managing Conflict to learn how to make peace with conflict and make it an organizational asset. Order Now!
Your comments are welcome
Would you like to see your comments posted here? rbrendPtoGuFOkTSMQOzxner@ChacEgGqaylUnkmwIkkwoCanyon.comSend me your comments by email, or by Web form.About Point Lookout
 Thank you for reading this article. I hope you enjoyed it and
found it useful, and that you'll consider recommending it to a friend.
Thank you for reading this article. I hope you enjoyed it and
found it useful, and that you'll consider recommending it to a friend.
This article in its entirety was written by a human being. No machine intelligence was involved in any way.
Point Lookout is a free weekly email newsletter. Browse the archive of past issues. Subscribe for free.
Support Point Lookout by joining the Friends of Point Lookout, as an individual or as an organization.
Do you face a complex interpersonal situation? Send it in, anonymously if you like, and I'll give you my two cents.
Related articles
More articles on Conflict Management:
 Responding to Threats: II
Responding to Threats: II- When an exchange between individuals, or between an individual and a group, goes wrong, threats often
are either the cause or part of the results. If we know how to deal with threats — and how to
avoid and prevent them — we can help keep communications creative and constructive.
 Biological Mimicry and Workplace Bullying
Biological Mimicry and Workplace Bullying- When targets of bullies decide to stand up to their bullies, to end the harassment, they frequently
act before they're really ready. Here's a metaphor that explains the value of waiting for the right
time to act.
 Ethical Debate at Work: I
Ethical Debate at Work: I- When we decide issues at work on any basis other than the merits, we elevate the chances of making bad
decisions. Here are some guidelines for ethical debate.
 Covert Obstruction in Teams: I
Covert Obstruction in Teams: I- Some organizational initiatives are funded and progressing, despite opposition. They continue to confront
attempts to deprive them of resources or to limit their progress. When team members covertly obstruct
progress, what techniques do they use?
 Toxic Disrupters: Tactics
Toxic Disrupters: Tactics- Some people tend to disrupt meetings. Their motives vary, but they use techniques drawn from a limited
collection. Examples: they violate norms, demand attention, mess with the agenda, and sow distrust.
Response begins with recognizing their tactics.
See also Conflict Management and Workplace Politics for more related articles.
Forthcoming issues of Point Lookout
 Coming May 1: Antipatterns for Time-Constrained Communication: 2
Coming May 1: Antipatterns for Time-Constrained Communication: 2- Recognizing just a few patterns that can lead to miscommunication can reduce the incidence of miscommunications. Here's Part 2 of a collection of antipatterns that arise in communication under time pressure, emphasizing those that depend on content. Available here and by RSS on May 1.
- And on May 8: Antipatterns for Time-Constrained Communication: 3
- Recognizing just a few patterns that can lead to miscommunication can reduce the incidence of problems. Here is Part 3 of a collection of antipatterns that arise in technical communication under time pressure, emphasizing past experiences of participants. Available here and by RSS on May 8.
Coaching services
I offer email and telephone coaching at both corporate and individual rates. Contact Rick for details at rbrendPtoGuFOkTSMQOzxner@ChacEgGqaylUnkmwIkkwoCanyon.com or (650) 787-6475, or toll-free in the continental US at (866) 378-5470.
Get the ebook!
Past issues of Point Lookout are available in six ebooks:
- Get 2001-2 in Geese Don't Land on Twigs (PDF, )
- Get 2003-4 in Why Dogs Wag (PDF, )
- Get 2005-6 in Loopy Things We Do (PDF, )
- Get 2007-8 in Things We Believe That Maybe Aren't So True (PDF, )
- Get 2009-10 in The Questions Not Asked (PDF, )
- Get all of the first twelve years (2001-2012) in The Collected Issues of Point Lookout (PDF, )
Are you a writer, editor or publisher on deadline? Are you looking for an article that will get people talking and get compliments flying your way? You can have 500-1000 words in your inbox in one hour. License any article from this Web site. More info
Follow Rick
Recommend this issue to a friend
Send an email message to a friend
rbrendPtoGuFOkTSMQOzxner@ChacEgGqaylUnkmwIkkwoCanyon.comSend a message to Rick
![]() A Tip A Day feed
A Tip A Day feed
![]() Point Lookout weekly feed
Point Lookout weekly feed
 My blog, Technical Debt for Policymakers, offers
resources, insights, and conversations of interest to policymakers who are concerned with managing
technical debt within their organizations. Get the millstone of technical debt off the neck of your
organization!
My blog, Technical Debt for Policymakers, offers
resources, insights, and conversations of interest to policymakers who are concerned with managing
technical debt within their organizations. Get the millstone of technical debt off the neck of your
organization!