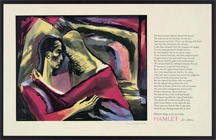
Polonius's Charge to Laertes, color wood engraving by Bernard Brussel-Smith (1914-1989). In Act I, Scene 3, of Shakespeare's Hamlet, Polonius, a courtier, dispenses some wisdom to his son. It is here that we find the now-famous lines, "Neither a borrower nor a lender be," "But not express'd in fancy, rich, not gaudy,/For the apparel oft proclaims the man," and "To thine own self be true." Photo courtesy U.S. Library of Congress.
Some call it "feedback." Some call it "criticism." Some try to distinguish the two, with varying degrees of success, but that's a topic for another time. By whatever name, we usually deliver the message with good intentions. When the intentions are good, but the results aren't, receivers are hurt, and givers surprised. To guard against this possibility, people have developed a number of introductory safety phrases.
One safety phrase is, "I'd like to give you some constructive criticism." It's almost an incantation — the magic words that are supposed to protect us from hurt or hurting others. But safety phrases, like incantations, don't always work as intended.
To achieve a positive outcome, givers need more than safety phrases — empathy is essential. To help givers of feedback or criticism understand the receiver's experience, I offer this framework for thinking about the entire process. By examining criticism from four perspectives — giver, receiver, content, and setting — we can develop guidelines for making criticism more effective. Here is Part I of those guidelines, emphasizing the giver and receiver.
- Investigate thoroughly and without bias
- It's just possible that the giver lacks access to important information that renders the criticism irrelevant, wrong, or worse. Delivering criticism that's clearly mistaken damages the giver's credibility. More important, it can damage the relationship between giver and receiver, perhaps permanently.
- The basis of any criticism must be thorough investigation. Sometimes, thoroughness requires the receiver's active participation. And sometimes, because people tend to adjust their responses based on the identity of the investigator, an unbiased investigation is possible only if performed by someone other than the giver.
- "To thine own self be true"
- If the giver's behavior or Criticizing the actions of someone
else, while you continue to do
similar things regularly yourself,
will likely contribute to
hostility in the relationshipbeliefs are similar to those the giver is criticizing, the receiver might feel anger, outrage, or pain, even if the giver's message is valid. Hostile feelings follow, in part, because criticism carries an implicit message that the giver isn't subject to similar criticism. - Criticizing the actions of someone else, while you continue to do similar things regularly yourself, will likely contribute to hostility in the relationship.
- Seek permission freely given
- If the receiver hasn't freely given the giver explicit or implicit permission to deliver criticism, then feelings of being attacked are likely. Even when permission has been given, the feeling of being attacked can come about if the permission wasn't given freely. For instance, accepting periodic performance reviews is actually a requirement of many jobs. The feeling of powerlessness in performance reviews comes about, in part, because performance reviews are mandatory.
- Delivering criticism without first gaining permission is unlikely to have a positive effect. Permission given under threat of employment termination, which is the context of most performance reviews, is not permission freely given. Permission sought and obtained in a public setting, where declining to give permission can be embarrassing or costly, probably is not permission freely given.
In Part II, we'll examine guidelines that arise from considering content and setting. ![]() Next issue in this series
Next issue in this series ![]() Top
Top ![]() Next Issue
Next Issue
Are you fed up with tense, explosive meetings? Are you or a colleague the target of a bully? Destructive conflict can ruin organizations. But if we believe that all conflict is destructive, and that we can somehow eliminate conflict, or that conflict is an enemy of productivity, then we're in conflict with Conflict itself. Read 101 Tips for Managing Conflict to learn how to make peace with conflict and make it an organizational asset. Order Now!
Your comments are welcome
Would you like to see your comments posted here? rbrenaXXxGCwVgbgLZDuRner@ChacDjdMAATPdDNJnrSwoCanyon.comSend me your comments by email, or by Web form.About Point Lookout
 Thank you for reading this article. I hope you enjoyed it and
found it useful, and that you'll consider recommending it to a friend.
Thank you for reading this article. I hope you enjoyed it and
found it useful, and that you'll consider recommending it to a friend.
This article in its entirety was written by a human being. No machine intelligence was involved in any way.
Point Lookout is a free weekly email newsletter. Browse the archive of past issues. Subscribe for free.
Support Point Lookout by joining the Friends of Point Lookout, as an individual or as an organization.
Do you face a complex interpersonal situation? Send it in, anonymously if you like, and I'll give you my two cents.
Related articles
More articles on Conflict Management:
 Masked Messages
Masked Messages- Sometimes what we say to each other isn't what we really mean. We mask the messages, or we form them
into what are usually positive structures, to make them appear to be something less malicious than they
are. Here are some examples of masked messages.
 Covert Bullying
Covert Bullying- The workplace bully is a tragically familiar figure to many. Bullying is costly to organizations, and
painful to everyone within them — especially targets. But the situation is worse than many realize,
because much bullying is covert. Here are some of the methods of covert bullies.
 On Snitching at Work: I
On Snitching at Work: I- Some people have difficulty determining the propriety of reporting violations to authorities at work.
Proper or not, reporting violations can be simultaneously both risky and necessary.
 What Do We Actually Know?
What Do We Actually Know?- Precision in both writing and speech can be critical in determining the success of collaborations in
the modern workplace. Precision is especially important when we distinguish between what we surmise
or assume and what we actually know.
 Storming: Obstacle or Pathway?
Storming: Obstacle or Pathway?- The Storming stage of Tuckman's model of small group development is widely misunderstood. Fighting the
storms, denying they exist, or bypassing them doesn't work. Letting them blow themselves out in a somewhat-controlled
manner is the path to Norming and Performing.
See also Conflict Management for more related articles.
Forthcoming issues of Point Lookout
 Coming October 1: On the Risks of Obscuring Ignorance
Coming October 1: On the Risks of Obscuring Ignorance- When people hide their ignorance of concepts fundamental to understanding the issues at hand, they expose their teams and organizations to a risk of making wrong decisions. The organizational costs of the consequences of those decisions can be unlimited. Available here and by RSS on October 1.
 And on October 8: Responding to Workplace Bullying
And on October 8: Responding to Workplace Bullying- Effective responses to bullying sometimes include "pushback tactics" that can deter perpetrators from further bullying. Because perpetrators use some of these same tactics, some people have difficulty employing them. But the need is real. Pushing back works. Available here and by RSS on October 8.
Coaching services
I offer email and telephone coaching at both corporate and individual rates. Contact Rick for details at rbrenaXXxGCwVgbgLZDuRner@ChacDjdMAATPdDNJnrSwoCanyon.com or (650) 787-6475, or toll-free in the continental US at (866) 378-5470.
Get the ebook!
Past issues of Point Lookout are available in six ebooks:
- Get 2001-2 in Geese Don't Land on Twigs (PDF, )
- Get 2003-4 in Why Dogs Wag (PDF, )
- Get 2005-6 in Loopy Things We Do (PDF, )
- Get 2007-8 in Things We Believe That Maybe Aren't So True (PDF, )
- Get 2009-10 in The Questions Not Asked (PDF, )
- Get all of the first twelve years (2001-2012) in The Collected Issues of Point Lookout (PDF, )
Are you a writer, editor or publisher on deadline? Are you looking for an article that will get people talking and get compliments flying your way? You can have 500-1000 words in your inbox in one hour. License any article from this Web site. More info
Follow Rick
Recommend this issue to a friend
Send an email message to a friend
rbrenaXXxGCwVgbgLZDuRner@ChacDjdMAATPdDNJnrSwoCanyon.comSend a message to Rick
![]() A Tip A Day feed
A Tip A Day feed
![]() Point Lookout weekly feed
Point Lookout weekly feed
 My blog, Technical Debt for Policymakers, offers
resources, insights, and conversations of interest to policymakers who are concerned with managing
technical debt within their organizations. Get the millstone of technical debt off the neck of your
organization!
My blog, Technical Debt for Policymakers, offers
resources, insights, and conversations of interest to policymakers who are concerned with managing
technical debt within their organizations. Get the millstone of technical debt off the neck of your
organization!