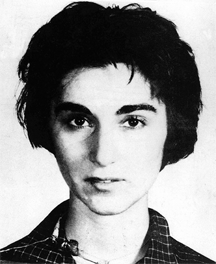
Kitty Genovese, in a mug shot created by the Queens, New York, police department after her arrest on a bookmaking charge in 1961. Ms. Genovese was murdered in the early hours of March 13, 1964, on her way home after work as a bartender. The New York Times reported, erroneously, that her murder was seen or heard by 38 individuals, none of whom called police to report the attack. The supposed incident became the basis for sociological research regarding the bystander effect. Although the bystander effect is real, and although the murder did occur, the reports of bystanders failing to report the attack on Ms. Genovese were false. Photo courtesy Wikipedia.
When we request information or action from others using email to convey the request, we are too often disappointed by the length of time required to receive a response, if in fact we do receive a response. Most people tend to lay the responsibility for this disappointing performance at the feet of the recipient of the request, and sometimes that is justified. But I believe that some of the responsibility belongs to the requestor. There are phrases and patterns we use that enable recipients to make choices that are inconsistent with our expectations.
In this post I review some of those nonconstructive patterns, and suggest alternatives that might improve communication between sender and recipient. In what follows I'll use the name Sam for the Sender, and Rocky for the Recipient. And when I refer to Sam (or Rocky) I'm referring only to some senders (or some recipients). Here are some phrases or patterns that I believe do depress the probability of satisfactory results.
- Let me know if "X"
- This construction seems like a straightforward There are phrases and patterns we
use in email that enable recipients
to make choices that are
inconsistent with our expectationsrequest to reply about something affected by the status of X. Sam expects that if X has happened, Rocky will respond about the situation in that case, and if X hasn't happened, Rocky will respond about that case. - But Sam's expectations might not be consistent with Rocky's interpretation of Sam's request. Rocky might interpret the request as, "If X then tell Sam X happened. Otherwise there is no need to do anything." And so, if X doesn't happen, Rocky doesn't reply, and Sam sits waiting for a reply that never comes.
- The fix for this is simple. Sam could instead send the message, "Let me know what's happening whether X or not X."
- Absence of "please"
- The "tone of voice" in senders' heads as they compose their messages isn't always the same as the "tone of voice" in recipients' heads as they read those same messages. Some recipients experience messages as rude even though they weren't meant to be rude at all. When this happens, some recipients decide to intentionally delay their responses.
- Adding a please to a request reduces (but doesn't eliminate) the incidence of unintended rudeness.
- Indirect questions
- A direct question in an email message is of the form, "When did the requisition go out?" An indirect question is a statement about a direct question, as in, "I'm curious about when the requisition went out." When Sam includes an indirect question in the message, Rocky might not feel compelled to respond to it.
- If you have a question, ask it directly.
- "Do you agree?" and other yes-or-no questions
- When Sam's message contains a yes-or-no question, Rocky is more likely to answer yes or no or something equally terse, even when Sam actually wants a more informative reply. For example, Sam might ask, "Has the requisition gone out yet?" What Sam really wants to know is more like, "When (date/time) did the requisition go out?"
- There are people who will supply terse responses to whatever questions you ask, but you're more likely to get the information you actually want if you actually ask for it.
- Omitting the deadline
- If Sam needs a response by the close of business today, but doesn't include that important fact in the message to Rocky, then Rocky is free to delay responding until tomorrow (or beyond).
- By including the preferred response timeframe in email requests, Sam provides the guidance Rocky needs for setting response priorities.
- Too many addressees
- The chance of receiving a helpful response to an email request can be affected by the number of addressees who receive the message. Research by Barron and Yechiam has shown that compared to responses to messages with multiple addressees, responses to messages addressed to a single recipient are more numerous, more helpful, and lengthier. [Barron & Yechiam 2002]
- This phenomenon is believed to be related to the bystander effect, which causes us to be less likely to lend assistance when others are present who could also lend assistance. [Fischer 2011] Also related is extensive work on diffusion of responsibility, though the research on that phenomenon does emphasize emergencies. [Darley & Latané 1968]
- The addressee was in the CC field
- If Sam sends a request to multiple people, the addressees in the CC field are less likely to respond to Sam's request than others are.
- To some people, "CC" is equivalent to "FYI" (For Your Information — no action required). Take care, because addresses sometimes appear in the CC field even when the sender didn't make a conscious choice to put them there. For example, suppose that Sam is replying to a message that was sent to multiple recipients. If Sam issues a "Reply All" command, most email clients would insert in the CC field the addresses of all recipients other than the sender of the original message and possibly Sam. To reply to a message sent to multiple recipients, with only selected recipients in the CC field, the sender must manually move the other CCd addressees to the To field.
- But a personal message to each individual is more effective. See "Too many addressees" above.
There are some more fundamental reasons why people might not respond to email requests. Many messages are too long, too ambiguous, and contain too many requests. Keep it simple, make it clear, and focus on what's most important. ![]() Top
Top ![]() Next Issue
Next Issue
Are you so buried in email that you don't even have time to delete your spam? Do you miss important messages? So many of the problems we have with email are actually within our power to solve, if we just realize the consequences of our own actions. Read 101 Tips for Writing and Managing Email to learn how to make peace with your inbox. Order Now!
And if you have organizational responsibility, you can help transform the culture to make more effective use of email. You can reduce volume while you make content more valuable. You can discourage email flame wars and that blizzard of useless if well-intended messages from colleagues and subordinates. Read Where There's Smoke There's Email to learn how to make email more productive at the organizational scale — and less dangerous. Order Now!
Footnotes
Your comments are welcome
Would you like to see your comments posted here? rbrenaXXxGCwVgbgLZDuRner@ChacDjdMAATPdDNJnrSwoCanyon.comSend me your comments by email, or by Web form.About Point Lookout
 Thank you for reading this article. I hope you enjoyed it and
found it useful, and that you'll consider recommending it to a friend.
Thank you for reading this article. I hope you enjoyed it and
found it useful, and that you'll consider recommending it to a friend.
This article in its entirety was written by a human being. No machine intelligence was involved in any way.
Point Lookout is a free weekly email newsletter. Browse the archive of past issues. Subscribe for free.
Support Point Lookout by joining the Friends of Point Lookout, as an individual or as an organization.
Do you face a complex interpersonal situation? Send it in, anonymously if you like, and I'll give you my two cents.
Related articles
More articles on Writing and Managing Email:
 Avoid Typing Under the Influence
Avoid Typing Under the Influence- When we communicate, we can't control how other people interpret our communications. Accidental offense
is inevitable, and email is especially likely to produce examples of this problem. What can we do as
members of electronic communities when trouble erupts?
 Email Antics: I
Email Antics: I- Nearly everyone I know complains that email is a time waster. Yet much of the problem results from our
own actions. If you're looking around for some New Year's resolutions to make, here are some ideas,
in this Part I of a little catalog of things we do that help waste our time.
 Email Antics: III
Email Antics: III- Nearly everyone complains that email is a time waster. Yet much of the problem results from our own
actions. Here's Part III of a little catalog of things we do that help waste our time.
 Email Antics: IV
Email Antics: IV- Nearly everyone I know complains that email is a real time waster. Yet much of the problem results from
our own actions. Here's Part IV of a little catalog of things we do that help waste our time.
 Four Overlooked Email Risks: II
Four Overlooked Email Risks: II- Email exchanges are notorious for exposing groups to battles that would never occur in face-to-face
conversation. But email has other limitations, less-often discussed, that make managing dialog very
difficult. Here's Part II of an exploration of some of those risks.
See also Writing and Managing Email for more related articles.
Forthcoming issues of Point Lookout
 Coming October 1: On the Risks of Obscuring Ignorance
Coming October 1: On the Risks of Obscuring Ignorance- A common dilemma in knowledge-based organizations: ask for an explanation, or "fake it" until you can somehow figure it out. The choice between admitting your own ignorance or obscuring it can be a difficult one. It has consequences for both the choice-maker and the organization. Available here and by RSS on October 1.
 And on October 8: Responding to Workplace Bullying
And on October 8: Responding to Workplace Bullying- Effective responses to bullying sometimes include "pushback tactics" that can deter perpetrators from further bullying. Because perpetrators use some of these same tactics, some people have difficulty employing them. But the need is real. Pushing back works. Available here and by RSS on October 8.
Coaching services
I offer email and telephone coaching at both corporate and individual rates. Contact Rick for details at rbrenaXXxGCwVgbgLZDuRner@ChacDjdMAATPdDNJnrSwoCanyon.com or (650) 787-6475, or toll-free in the continental US at (866) 378-5470.
Get the ebook!
Past issues of Point Lookout are available in six ebooks:
- Get 2001-2 in Geese Don't Land on Twigs (PDF, )
- Get 2003-4 in Why Dogs Wag (PDF, )
- Get 2005-6 in Loopy Things We Do (PDF, )
- Get 2007-8 in Things We Believe That Maybe Aren't So True (PDF, )
- Get 2009-10 in The Questions Not Asked (PDF, )
- Get all of the first twelve years (2001-2012) in The Collected Issues of Point Lookout (PDF, )
Are you a writer, editor or publisher on deadline? Are you looking for an article that will get people talking and get compliments flying your way? You can have 500-1000 words in your inbox in one hour. License any article from this Web site. More info
Follow Rick
Recommend this issue to a friend
Send an email message to a friend
rbrenaXXxGCwVgbgLZDuRner@ChacDjdMAATPdDNJnrSwoCanyon.comSend a message to Rick
![]() A Tip A Day feed
A Tip A Day feed
![]() Point Lookout weekly feed
Point Lookout weekly feed
 My blog, Technical Debt for Policymakers, offers
resources, insights, and conversations of interest to policymakers who are concerned with managing
technical debt within their organizations. Get the millstone of technical debt off the neck of your
organization!
My blog, Technical Debt for Policymakers, offers
resources, insights, and conversations of interest to policymakers who are concerned with managing
technical debt within their organizations. Get the millstone of technical debt off the neck of your
organization!