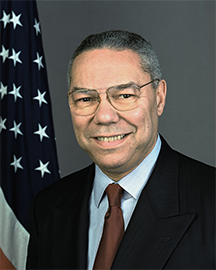
Official portrait of Colin L. Powell as the Secretary of State of the United States of America, taken in January 2001. One incident in his career serves to illustrate the full complexity of the "Hit and Run" model of career decisions. Shortly after the 2004 U.S. Presidential election, when the administration of George W. Bush was still near its zenith in popularity and confidence, Secretary Powell resigned his position. Not all resignations are examples of "Hit and Run," but some are motivated by knowledge of trouble looming in the near future. We cannot know whether Secretary Powell's decision was so motivated, but in retrospect, it is consistent with a closely related variant of "Hit and Run" that one might call "It's Your Ball," (or "Be My Guest" or "Knock Yourself Out") in its positive form, or "Jumping Ship" in a more disreputable form. Secretary Powell's well-established record of integrity suggests that if anything, his decision might best fit "It's Your Ball." Photo by U.S. Department of State courtesy Wikimedia Commons.
When political operators uses toxic tactics at work, we need not respond by descending into the pit right alongside them. Responding ethically and with integrity is almost always possible, if we can detect the devious tactics early enough. Here's a collection of fairly widely used political tactics, with some suggestions for ethical, but politically savvy, responses.
- Hit and Run
- When someone moves on from one high profile activity to another while the current effort is still underway, he or she might have knowledge (or suspect) that the current effort is at risk or doomed. Soon afterward, the project implodes, but the operator isn't charged, and often claims that the then-current owners of the activity are at fault.
- If a project in your organization implodes dramatically, just after the departure of its leader or champion, investigate carefully before calling on her or him to rescue the project. Rule out "Hit and Run" before you get hit again.
- The proxy target
- Sometimes an attacker's true target isn't the person who's attacked. Rather, it could be the supervisor or mentor of the person attacked. By attacking the proxy target, the attacker diverts the attention of the true target, and might even harm the true target's reputation.
- When attacked by someone much more powerful than yourself, don't assume that you're the true target. You could be a proxy. The harm done to you might be just as real, but knowing what's actually happening can be extremely helpful in formulating a response.
- Confidential disinformation
- When we confide in one another, the confider usually believes what is confided. That's one reason why we tend to believe what others tell us in confidence. Enhanced credibility explains, in part, why political operators sometimes tell lies — or partial truths — in confidence. And they also gain the protection of secrecy and deniability.
- Don't assume that confiders believe everything they tell you in confidence. Verify and validate when you can.
- The favored subordinate
- Supervisors sometimes designate a favored subordinate who receives extra attention, multiple benefits, and who can seemingly do no wrong. Especially when this designation results from supervisor initiative — that is, when the designee hasn't curried favor — the supervisor has acknowledged and usually accepts the possibility that other subordinates will become resentful or demoralized.
- Whether or not the favored When someone moves on from
one high profile activity to another
while the current effort is still
underway, he or she might know
that the current effort
is at risk or doomedsubordinate has sought special status, it's likely that the supervisor's intentional choice is a signal to other subordinates that they must either accept secondary status, or move on. Because there are rarely any limits to how secondary that secondary status will be, it's probably best to move on. You lose little, though, because the favored position is usually just another form of subordination, maintained only at the price of freedom and dignity.
Detecting these patterns in our own situations can be difficult, because we don't want to find them. Look for them first in the situations others face. When you become adept at spotting them there, examine your own. ![]() Top
Top ![]() Next Issue
Next Issue
Is every other day a tense, anxious, angry misery as you watch people around you, who couldn't even think their way through a game of Jacks, win at workplace politics and steal the credit and glory for just about everyone's best work including yours? Read 303 Secrets of Workplace Politics, filled with tips and techniques for succeeding in workplace politics. More info
For more devious political tactics, check out the archive Devious Political Tactics.
Your comments are welcome
Would you like to see your comments posted here? rbrenaXXxGCwVgbgLZDuRner@ChacDjdMAATPdDNJnrSwoCanyon.comSend me your comments by email, or by Web form.About Point Lookout
 Thank you for reading this article. I hope you enjoyed it and
found it useful, and that you'll consider recommending it to a friend.
Thank you for reading this article. I hope you enjoyed it and
found it useful, and that you'll consider recommending it to a friend.
This article in its entirety was written by a human being. No machine intelligence was involved in any way.
Point Lookout is a free weekly email newsletter. Browse the archive of past issues. Subscribe for free.
Support Point Lookout by joining the Friends of Point Lookout, as an individual or as an organization.
Do you face a complex interpersonal situation? Send it in, anonymously if you like, and I'll give you my two cents.
Related articles
More articles on Workplace Politics:
 The Advantages of Political Attack: II
The Advantages of Political Attack: II- In workplace politics, attackers are often surprisingly successful with even the flimsiest assertions.
Often, they prevail, in part, because they can choose the time and venue for their attacks. They also
have the advantage of preparation. How can targets respond effectively?
 Social Transactions: We're Doing It My Way
Social Transactions: We're Doing It My Way- We have choices about how we conduct social transactions — greetings, partings, opening doors,
and so on. Some transactions require that we collaborate with others. In social transactions, how do
we decide whose preferences rule?
 Some Hazards of Skip-Level Interviews: III
Some Hazards of Skip-Level Interviews: III- Skip-level interviews — dialogs between a subordinate and the subordinate's supervisor's supervisor
— can be hazardous. Here's Part III of a little catalog of the hazards, emphasizing subordinate-initiated
skip-level interviews.
 Exploiting Functional Fixedness: II
Exploiting Functional Fixedness: II- A cognitive bias called functional fixedness causes difficulty in recognizing new uses for
familiar things. It also makes for difficulty in recognizing devious uses of everyday behaviors. Here's
Part II of a catalog of deviousness based on functional fixedness.
 Self-Importance and Conversational Narcissism at Work: II
Self-Importance and Conversational Narcissism at Work: II- Self-importance is one of four major themes of conversational narcissism. Knowing how to recognize the
patterns of conversational narcissism is a fundamental skill needed for controlling it. Here are eight
examples that emphasize self-importance.
See also Workplace Politics for more related articles.
Forthcoming issues of Point Lookout
 Coming October 1: On the Risks of Obscuring Ignorance
Coming October 1: On the Risks of Obscuring Ignorance- A common dilemma in knowledge-based organizations: ask for an explanation, or "fake it" until you can somehow figure it out. The choice between admitting your own ignorance or obscuring it can be a difficult one. It has consequences for both the choice-maker and the organization. Available here and by RSS on October 1.
 And on October 8: Responding to Workplace Bullying
And on October 8: Responding to Workplace Bullying- Effective responses to bullying sometimes include "pushback tactics" that can deter perpetrators from further bullying. Because perpetrators use some of these same tactics, some people have difficulty employing them. But the need is real. Pushing back works. Available here and by RSS on October 8.
Coaching services
I offer email and telephone coaching at both corporate and individual rates. Contact Rick for details at rbrenaXXxGCwVgbgLZDuRner@ChacDjdMAATPdDNJnrSwoCanyon.com or (650) 787-6475, or toll-free in the continental US at (866) 378-5470.
Get the ebook!
Past issues of Point Lookout are available in six ebooks:
- Get 2001-2 in Geese Don't Land on Twigs (PDF, )
- Get 2003-4 in Why Dogs Wag (PDF, )
- Get 2005-6 in Loopy Things We Do (PDF, )
- Get 2007-8 in Things We Believe That Maybe Aren't So True (PDF, )
- Get 2009-10 in The Questions Not Asked (PDF, )
- Get all of the first twelve years (2001-2012) in The Collected Issues of Point Lookout (PDF, )
Are you a writer, editor or publisher on deadline? Are you looking for an article that will get people talking and get compliments flying your way? You can have 500-1000 words in your inbox in one hour. License any article from this Web site. More info
Follow Rick
Recommend this issue to a friend
Send an email message to a friend
rbrenaXXxGCwVgbgLZDuRner@ChacDjdMAATPdDNJnrSwoCanyon.comSend a message to Rick
![]() A Tip A Day feed
A Tip A Day feed
![]() Point Lookout weekly feed
Point Lookout weekly feed
 My blog, Technical Debt for Policymakers, offers
resources, insights, and conversations of interest to policymakers who are concerned with managing
technical debt within their organizations. Get the millstone of technical debt off the neck of your
organization!
My blog, Technical Debt for Policymakers, offers
resources, insights, and conversations of interest to policymakers who are concerned with managing
technical debt within their organizations. Get the millstone of technical debt off the neck of your
organization!Beware any resource that speaks of "winning" at workplace politics or "defeating" it. You can benefit or not, but there is no score-keeping, and it isn't a game.
- Wikipedia has a nice article with a list of additional resources
- Some public libraries offer collections. Here's an example from Saskatoon.
- Check my own links collection
- LinkedIn's Office Politics discussion group
