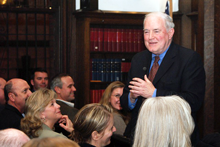
Professor Brian Kelley, retired CIA officer, speaking at The Institute of World Politics to students, faculty, and friends, on the "story behind the story" of the investigation of former FBI agent Robert Hanssen, who spied for the Soviet and Russian intelligence services from 1979 to 2001. For years, Prof. Kelley himself had been the prime suspect in a series of incidents that were actually the work of Hanssen's espionage. In November of 1998, investigators attempted to trap Kelley using a disinformation tactic. They had a man with a foreign accent come to Kelley's door and warn him that the FBI knew he was a spy. The man told him to go to a specific Metro station the next day to escape. The strategy was designed to prove Kelley's guilt by trapping him into trying to escape. Kelley instead reported the incident to the FBI, but that didn't ease the investigators' suspicions. Kelley and his family were interrogated and he was put on administrative leave for almost two years, ending only with Hanssen's arrest based on evidence obtained elsewhere. Photo courtesy The Institute of World Politics.
Shredding documents, destroying or recycling hard drives, and altering records are examples of destroying evidence of what the organization is concealing. Even when evidence destruction is the primary concealment strategy, it's effective only if all evidence is destroyed or rendered unobtainable.
The testimony of witnesses is one kind of evidence that cannot be destroyed as long as the witnesses are able to bear witness. Testimony can be prevented by intimidation, brutality, bribery, and other means, but if prevention fails, what then? From the concealer's perspective, two techniques can be effective even if the whistleblower blows the whistle.
- Indirect personal attacks
- Most whistleblowers anticipate direct personal attacks, but personal attacks can be directed at loved ones, too. Children, spouses, parents, siblings — all are potential targets. Spouses can be seduced. Legal, emotional, financial, marital, or other difficulties of close family members can be exposed and used to discredit or apply pressure to whistleblowers.
- If you already know of vulnerabilities of this kind, consider carefully how to protect yourself. Finding employment elsewhere is not protection from those who fear exposure. If the organization or its employees believe that you might someday become a problem, they might preemptively destroy your credibility in advance of any action you might take, no matter where you go for your next job or assignment. Effective protection usually involves convincing them of your ability to do more damage to them than they can do to you. That strategy often requires assembling evidence and seeking professional assistance.
- Direct disinformation
- Employees not directly implicated Finding employment elsewhere
is not protection from
those who fear exposurein the concealed activity (or inactivity) are potential candidate whistleblowers, because they often feel — justifiably or not — that they haven't themselves transgressed. From the perspective of those directly involved, even candidate whistleblowers constitute risk. To limit risk, false information of a seemingly incriminating nature is sometimes made available to them. Passing along this disinformation to investigators or media could then damage the whistleblower's credibility. - Don't assume that everything you think you know about the concealed activity is actually true. Be especially careful about material that came to you too easily, or uncorroborated, or which had a "stage-managed" feel. If you suspect that you've received disinformation, interpret it as an indicator that you're being targeted proactively as a potential whistleblower. That could mean that the organization, or individuals within it, have taken other actions as well, such as investigating you or your family members, or tampering with your work products or records. When you do pass along information to counsel, investigators, or media, be careful to indicate whether you suspect that any of it is disinformation intentionally passed along to you.
These tactics are rarely obvious. Intuition and good judgment are required. Trust the Force, Luke. ![]() First issue in this series
First issue in this series ![]() Top
Top ![]() Next Issue
Next Issue
Is every other day a tense, anxious, angry misery as you watch people around you, who couldn't even think their way through a game of Jacks, win at workplace politics and steal the credit and glory for just about everyone's best work including yours? Read 303 Secrets of Workplace Politics, filled with tips and techniques for succeeding in workplace politics. More info
Your comments are welcome
Would you like to see your comments posted here? rbrenaXXxGCwVgbgLZDuRner@ChacDjdMAATPdDNJnrSwoCanyon.comSend me your comments by email, or by Web form.About Point Lookout
 Thank you for reading this article. I hope you enjoyed it and
found it useful, and that you'll consider recommending it to a friend.
Thank you for reading this article. I hope you enjoyed it and
found it useful, and that you'll consider recommending it to a friend.
This article in its entirety was written by a human being. No machine intelligence was involved in any way.
Point Lookout is a free weekly email newsletter. Browse the archive of past issues. Subscribe for free.
Support Point Lookout by joining the Friends of Point Lookout, as an individual or as an organization.
Do you face a complex interpersonal situation? Send it in, anonymously if you like, and I'll give you my two cents.
Related articles
More articles on Workplace Politics:
 How to Avoid Responsibility
How to Avoid Responsibility- Taking responsibility and a willingness to be held accountable are the hallmarks of either a rising
star in a high-performance organization, or a naïve fool in a low-performance organization. Either
way, you must know the more popular techniques for avoiding responsibility.
 Devious Political Tactics: Mis- and Disinformation
Devious Political Tactics: Mis- and Disinformation- Practitioners of workplace politics intent on gaining unfair advantage sometimes use misinformation,
disinformation, and other information-related tactics. Here's a short catalog of techniques to watch for.
 On Snitching at Work: I
On Snitching at Work: I- Some people have difficulty determining the propriety of reporting violations to authorities at work.
Proper or not, reporting violations can be simultaneously both risky and necessary.
 Impasses in Group Decision Making: III
Impasses in Group Decision Making: III- In group decision making, impasses can develop. Some are related to the substance of the issue at hand.
With some effort, we can usually resolve substantive impasses. But treating nonsubstantive impasses
in the same way doesn't work. Here's why.
 High Falutin' Goofy Talk: III
High Falutin' Goofy Talk: III- Workplace speech and writing sometimes strays into the land of pretentious but overused business phrases,
which I like to call "high falutin' goofy talk." We use these phrases with perhaps less thought
than they deserve, because they can be trite or can evoke indecorous images. Here's Part III of a collection
of phrases and images to avoid.
See also Workplace Politics for more related articles.
Forthcoming issues of Point Lookout
 Coming October 1: On the Risks of Obscuring Ignorance
Coming October 1: On the Risks of Obscuring Ignorance- A common dilemma in knowledge-based organizations: ask for an explanation, or "fake it" until you can somehow figure it out. The choice between admitting your own ignorance or obscuring it can be a difficult one. It has consequences for both the choice-maker and the organization. Available here and by RSS on October 1.
 And on October 8: Responding to Workplace Bullying
And on October 8: Responding to Workplace Bullying- Effective responses to bullying sometimes include "pushback tactics" that can deter perpetrators from further bullying. Because perpetrators use some of these same tactics, some people have difficulty employing them. But the need is real. Pushing back works. Available here and by RSS on October 8.
Coaching services
I offer email and telephone coaching at both corporate and individual rates. Contact Rick for details at rbrenaXXxGCwVgbgLZDuRner@ChacDjdMAATPdDNJnrSwoCanyon.com or (650) 787-6475, or toll-free in the continental US at (866) 378-5470.
Get the ebook!
Past issues of Point Lookout are available in six ebooks:
- Get 2001-2 in Geese Don't Land on Twigs (PDF, )
- Get 2003-4 in Why Dogs Wag (PDF, )
- Get 2005-6 in Loopy Things We Do (PDF, )
- Get 2007-8 in Things We Believe That Maybe Aren't So True (PDF, )
- Get 2009-10 in The Questions Not Asked (PDF, )
- Get all of the first twelve years (2001-2012) in The Collected Issues of Point Lookout (PDF, )
Are you a writer, editor or publisher on deadline? Are you looking for an article that will get people talking and get compliments flying your way? You can have 500-1000 words in your inbox in one hour. License any article from this Web site. More info
Follow Rick
Recommend this issue to a friend
Send an email message to a friend
rbrenaXXxGCwVgbgLZDuRner@ChacDjdMAATPdDNJnrSwoCanyon.comSend a message to Rick
![]() A Tip A Day feed
A Tip A Day feed
![]() Point Lookout weekly feed
Point Lookout weekly feed
 My blog, Technical Debt for Policymakers, offers
resources, insights, and conversations of interest to policymakers who are concerned with managing
technical debt within their organizations. Get the millstone of technical debt off the neck of your
organization!
My blog, Technical Debt for Policymakers, offers
resources, insights, and conversations of interest to policymakers who are concerned with managing
technical debt within their organizations. Get the millstone of technical debt off the neck of your
organization!Beware any resource that speaks of "winning" at workplace politics or "defeating" it. You can benefit or not, but there is no score-keeping, and it isn't a game.
- Wikipedia has a nice article with a list of additional resources
- Some public libraries offer collections. Here's an example from Saskatoon.
- Check my own links collection
- LinkedIn's Office Politics discussion group
