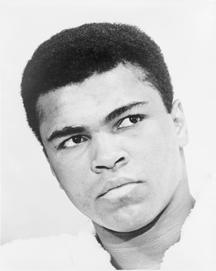
Muhammad Ali in 1967, seven years before the George Foreman match in Kinshasa. At the time of the match, experts considered Ali's strengths to be speed and technical skill. Foreman, a gold medalist in the 1968 Olympics, was considered dominant in power and size. Moreover, since at 32 Ali was a week short of seven years older than Foreman, Ali's strengths were considered to be fading on account of age. Although Foreman was heavily favored, Ali defeated him by a knockout. It was Foreman's first defeat, and it remains his only loss by a knockout. Photo by Ira Rosenberg, a staff photographer at New York World-Telegram and Sun. It is part of a collection donated to the U.S. Library of Congress, Prints and Photographs division, under the digital ID cph.3c1543.
In organizational politics, most attack strategies assume accurate predictions of the defender's response. Since unsophisticated attackers tend to leave options open for defenders, finding suitable defense strategies is relatively straightforward. But sophisticated attackers usually try to gain control of the defender's choices to reduce uncertainty about the outcome. The sophisticated attack is therefore the interesting case.
For sophisticated attacks, unexpected responses are preferable. One response that's often effective is "rope-a-dope." The term was first applied to Mohammed Ali's strategy in a boxing match with then heavyweight champion George Foreman, on October 30, 1974, in Kinshasa. After letting Foreman tire on the attack, Ali won by a knockout in the eighth round.
The strength of "rope-a-dope" is its focus on the long time scale. Foreman was thinking on the time scale of the jab or punch, or at most, several combinations. Ali was thinking on the time scale of several rounds. Ali's strategy was to withstand blows while Foreman exhausted himself, and then switch to offense.
In organizational politics, attackers tend to focus on the same time scale as their attacks. They try to control the defender's immediate response options, emphasizing especially those responses that could harm the attacker and eventually give the defender the initiative.
A rope-a-dope response to political attacks first emphasizes withstanding the attacks long enough to render the attacker incapable of effective defense. Only then does the defender go to the offense.
For example, suppose Hannibal, the attacker and more powerful, is the leader of H-Division. Hannibal seeks to acquire C-Division, headed by Clarice, the defender and less powerful. Hannibal intends to terminate Clarice, and then install policies that decrease sales of C-Division's products, some of which embarrass H-Division because of their superiority.
Defenders usually try to make the most cogent rational case for retaining the status quo. Because logic is less effective than political power, they rarely succeed. For instance, the attacker might have prepared the ground by having pre-positioned persuasive rational arguments — sometimes based on misrepresentations — outside the defender's awareness.
The rope-a-dope response to such an attack has three steps:
- Enhance situational awareness
- Enhance In organizational politics, attackers
tend to focus on the same
time scale as their attacksdetection of the attacker's pre-positioning of rational arguments for acquiring and eventually dismembering the defending organization. Using this knowledge, adjust C-Division's activities, and prepare — but don't deliver — counterclaims and refutations of Hannibal's claims. - Produce a superior, high-value, high-visibility product
- Produce a product that's based on strong customer relationships, and which cannot be replicated outside C-Division, because it depends on the division's continued existence, intact. This ploy secures organizational longevity, even if H-Division acquires C-Division.
- Seize the initiative
- After the acquisition, when Hannibal's exaggerated claims are beginning to crumble, release the previously crafted refutations and counterclaims.
Rope-a-dope strategies can be risky. They require patience and nerve. But defeat is even less appealing. ![]() Top
Top ![]() Next Issue
Next Issue
Is every other day a tense, anxious, angry misery as you watch people around you, who couldn't even think their way through a game of Jacks, win at workplace politics and steal the credit and glory for just about everyone's best work including yours? Read 303 Secrets of Workplace Politics, filled with tips and techniques for succeeding in workplace politics. More info
Your comments are welcome
Would you like to see your comments posted here? rbrenaXXxGCwVgbgLZDuRner@ChacDjdMAATPdDNJnrSwoCanyon.comSend me your comments by email, or by Web form.About Point Lookout
 Thank you for reading this article. I hope you enjoyed it and
found it useful, and that you'll consider recommending it to a friend.
Thank you for reading this article. I hope you enjoyed it and
found it useful, and that you'll consider recommending it to a friend.
This article in its entirety was written by a human being. No machine intelligence was involved in any way.
Point Lookout is a free weekly email newsletter. Browse the archive of past issues. Subscribe for free.
Support Point Lookout by joining the Friends of Point Lookout, as an individual or as an organization.
Do you face a complex interpersonal situation? Send it in, anonymously if you like, and I'll give you my two cents.
Related articles
More articles on Workplace Politics:
 Things We Believe That Maybe Aren't So True
Things We Believe That Maybe Aren't So True- Maxims and rules make life simpler by eliminating decisions. And they have a price: they sometimes foreclose
options that would have worked better than anything else. Here are some things we believe in maybe a
little too much.
 Organizational Loss: Searching Behavior
Organizational Loss: Searching Behavior- When organizations suffer painful losses, their responses can sometimes be destructive, further harming
the organization and its people. Here are some typical patterns of destructive responses to organizational
loss.
 Why Others Do What They Do
Why Others Do What They Do- If you're human, you make mistakes. A particularly expensive kind of mistake is guessing incorrectly
why others do what they do. Here are some of the ways we get this wrong.
 Career Opportunity or Career Trap: I
Career Opportunity or Career Trap: I- When we're presented with an opportunity that seems too good to be true, as the saying goes, it probably
is. Although it's easy to decline free vacations, declining career opportunities is another matter.
Here's a look at indicators that a career opportunity might be a career trap.
 Cyber Rumors in Organizations
Cyber Rumors in Organizations- Rumor management practices in organizations haven't kept up with rumor propagation technology. Rumors
that propagate by digital means — cyber rumors — have longer lifetimes, spread faster, are
more credible, and are better able to reinforce each other.
See also Workplace Politics for more related articles.
Forthcoming issues of Point Lookout
 Coming October 1: On the Risks of Obscuring Ignorance
Coming October 1: On the Risks of Obscuring Ignorance- When people hide their ignorance of concepts fundamental to understanding the issues at hand, they expose their teams and organizations to a risk of making wrong decisions. The organizational costs of the consequences of those decisions can be unlimited. Available here and by RSS on October 1.
 And on October 8: Responding to Workplace Bullying
And on October 8: Responding to Workplace Bullying- Effective responses to bullying sometimes include "pushback tactics" that can deter perpetrators from further bullying. Because perpetrators use some of these same tactics, some people have difficulty employing them. But the need is real. Pushing back works. Available here and by RSS on October 8.
Coaching services
I offer email and telephone coaching at both corporate and individual rates. Contact Rick for details at rbrenaXXxGCwVgbgLZDuRner@ChacDjdMAATPdDNJnrSwoCanyon.com or (650) 787-6475, or toll-free in the continental US at (866) 378-5470.
Get the ebook!
Past issues of Point Lookout are available in six ebooks:
- Get 2001-2 in Geese Don't Land on Twigs (PDF, )
- Get 2003-4 in Why Dogs Wag (PDF, )
- Get 2005-6 in Loopy Things We Do (PDF, )
- Get 2007-8 in Things We Believe That Maybe Aren't So True (PDF, )
- Get 2009-10 in The Questions Not Asked (PDF, )
- Get all of the first twelve years (2001-2012) in The Collected Issues of Point Lookout (PDF, )
Are you a writer, editor or publisher on deadline? Are you looking for an article that will get people talking and get compliments flying your way? You can have 500-1000 words in your inbox in one hour. License any article from this Web site. More info
Follow Rick
Recommend this issue to a friend
Send an email message to a friend
rbrenaXXxGCwVgbgLZDuRner@ChacDjdMAATPdDNJnrSwoCanyon.comSend a message to Rick
![]() A Tip A Day feed
A Tip A Day feed
![]() Point Lookout weekly feed
Point Lookout weekly feed
 My blog, Technical Debt for Policymakers, offers
resources, insights, and conversations of interest to policymakers who are concerned with managing
technical debt within their organizations. Get the millstone of technical debt off the neck of your
organization!
My blog, Technical Debt for Policymakers, offers
resources, insights, and conversations of interest to policymakers who are concerned with managing
technical debt within their organizations. Get the millstone of technical debt off the neck of your
organization!Beware any resource that speaks of "winning" at workplace politics or "defeating" it. You can benefit or not, but there is no score-keeping, and it isn't a game.
- Wikipedia has a nice article with a list of additional resources
- Some public libraries offer collections. Here's an example from Saskatoon.
- Check my own links collection
- LinkedIn's Office Politics discussion group
