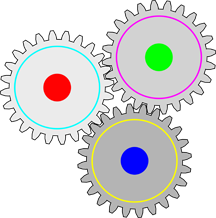
Three gears in a configuration that's inherently locked up. Any combination of an odd number of planar gears configured in a loop is inherently locked. Email exchanges about complex dynamic topics aren't inherently locked up, but the probability of dysfunction increases as the time scale of changes in the substance of the topic decreases to and then drops below the end-to-end latency maximized over all participants. Image by J_Alves.
When we work together to resolve issues or make decisions, or even to gather information, we engage in a series of exchanges. We ask and respond to questions, report status, propose explanations, provide opinions, and much more. We do this in email, by teleconference, in face-to-face meetings, and at times, by text message. One exchange can even span several of these media. But because so many of us are moving targets, email has become a primary means of carrying out these exchanges. It's so dominant that we use it even when we don't need to, and that's where the trouble begins.
Exchanging email is a kind of conversing, but it differs from telephone and face-to-face conversation in important ways. Email doesn't represent emotive content faithfully; the writing skills of authors of email are variable; and authors tend to dash off messages without careful thought. I could go on.
But four properties of email exchanges expose participants to elevated risk of making wrong decisions. These four receive much less attention than they deserve. Here in Part I are two of these properties.
- End-to-end latency
- In the context of email exchanges, latency is usually defined as the time between origination and receipt of a contribution to the conversation. We can call this form of latency transmission latency. It can differ for different participants. Perhaps more significantly, and more usefully, latency could be defined as the time between the author's conceiving a contribution and the recipient's reading it. We can call this kind of latency end-to-end latency. What happens during the end-to-end latency period includes all transmission delay, but also delays caused by workplace interruptions, offsets in the sleep-wake cycle, urgent demands for the attention of authors and recipients, and other factors.
- In some Email exchanges are unlike
in-person conversations.
Time delays can
have severe effects.instances, end-to-end latency can be infinite. This happens when spam filtering blocks or quarantines messages; when authors intend to contribute but fail to do so for some reason; when recipient errors or high incoming email volume cause recipients to overlook messages; or when recipients misinterpret messages and on that faulty basis elect not to respond. - Duration of message content validity
- In synchronous meetings — face-to-face, live video, or telephone — when a participant's contribution is invalid in some respects, other participants can offer corrections almost immediately or relatively quickly. The original contributor might then either dispute or accept the correction, equally immediately. Invalid contributions have relatively short lifetimes.
- By contrast, in email exchanges, invalid contributions can have longer — sometimes much longer — effective lifetimes, because of the longer end-to-end latency of email messages. And during the time in which the invalid content is extant, it can spin off additional content that itself can be invalid. When contributions correcting the original message finally appear, the original poster might not see them immediately, which further delays final resolution of the issue.
We'll continue next time with two additional familiar, but less-often discussed properties of email exchanges. ![]() Next issue in this series
Next issue in this series ![]() Top
Top ![]() Next Issue
Next Issue
Are you so buried in email that you don't even have time to delete your spam? Do you miss important messages? So many of the problems we have with email are actually within our power to solve, if we just realize the consequences of our own actions. Read 101 Tips for Writing and Managing Email to learn how to make peace with your inbox. Order Now!
And if you have organizational responsibility, you can help transform the culture to make more effective use of email. You can reduce volume while you make content more valuable. You can discourage email flame wars and that blizzard of useless if well-intended messages from colleagues and subordinates. Read Where There's Smoke There's Email to learn how to make email more productive at the organizational scale — and less dangerous. Order Now!
Your comments are welcome
Would you like to see your comments posted here? rbrenaXXxGCwVgbgLZDuRner@ChacDjdMAATPdDNJnrSwoCanyon.comSend me your comments by email, or by Web form.About Point Lookout
 Thank you for reading this article. I hope you enjoyed it and
found it useful, and that you'll consider recommending it to a friend.
Thank you for reading this article. I hope you enjoyed it and
found it useful, and that you'll consider recommending it to a friend.
This article in its entirety was written by a human being. No machine intelligence was involved in any way.
Point Lookout is a free weekly email newsletter. Browse the archive of past issues. Subscribe for free.
Support Point Lookout by joining the Friends of Point Lookout, as an individual or as an organization.
Do you face a complex interpersonal situation? Send it in, anonymously if you like, and I'll give you my two cents.
Related articles
More articles on Effective Communication at Work:
 The Power of Presuppositions
The Power of Presuppositions- Presuppositions are powerful tools for manipulating others. To defend yourself, know how they're used,
know how to detect them, and know how to respond.
 Achieving Goals: Inspiring Passion and Action
Achieving Goals: Inspiring Passion and Action- Achieving your goals requires both passion and action. Knowing when to emphasize passion and when to
emphasize action are the keys to managing yourself, or others, toward achievement.
 Reframing Revision Resentment: I
Reframing Revision Resentment: I- From time to time, we're required to revise something previously produced — some copy, remarks,
an announcement, code, the Mona Lisa, whatever… When we do, some of us experience frustration,
and view the assignment as an onerous chore. Here are some alternative perspectives that might ease
the burden.
 Unintended Condescension: II
Unintended Condescension: II- Intentionally making condescending remarks is something most of us do only when we lose control. But
anyone at any time can inadvertently make a remark that someone else experiences as condescending. We
explored two patterns to avoid last time. Here are two more.
 Straw Man Variants
Straw Man Variants- The Straw Man fallacy is a famous rhetorical fallacy. Using it distorts debate and can lead groups to
reach faulty conclusions. It's readily recognized, but it has some variants that are more difficult
to spot. When unnoticed, trouble looms.
See also Effective Communication at Work for more related articles.
Forthcoming issues of Point Lookout
 Coming October 1: On the Risks of Obscuring Ignorance
Coming October 1: On the Risks of Obscuring Ignorance- A common dilemma in knowledge-based organizations: ask for an explanation, or "fake it" until you can somehow figure it out. The choice between admitting your own ignorance or obscuring it can be a difficult one. It has consequences for both the choice-maker and the organization. Available here and by RSS on October 1.
 And on October 8: Responding to Workplace Bullying
And on October 8: Responding to Workplace Bullying- Effective responses to bullying sometimes include "pushback tactics" that can deter perpetrators from further bullying. Because perpetrators use some of these same tactics, some people have difficulty employing them. But the need is real. Pushing back works. Available here and by RSS on October 8.
Coaching services
I offer email and telephone coaching at both corporate and individual rates. Contact Rick for details at rbrenaXXxGCwVgbgLZDuRner@ChacDjdMAATPdDNJnrSwoCanyon.com or (650) 787-6475, or toll-free in the continental US at (866) 378-5470.
Get the ebook!
Past issues of Point Lookout are available in six ebooks:
- Get 2001-2 in Geese Don't Land on Twigs (PDF, )
- Get 2003-4 in Why Dogs Wag (PDF, )
- Get 2005-6 in Loopy Things We Do (PDF, )
- Get 2007-8 in Things We Believe That Maybe Aren't So True (PDF, )
- Get 2009-10 in The Questions Not Asked (PDF, )
- Get all of the first twelve years (2001-2012) in The Collected Issues of Point Lookout (PDF, )
Are you a writer, editor or publisher on deadline? Are you looking for an article that will get people talking and get compliments flying your way? You can have 500-1000 words in your inbox in one hour. License any article from this Web site. More info
Follow Rick
Recommend this issue to a friend
Send an email message to a friend
rbrenaXXxGCwVgbgLZDuRner@ChacDjdMAATPdDNJnrSwoCanyon.comSend a message to Rick
![]() A Tip A Day feed
A Tip A Day feed
![]() Point Lookout weekly feed
Point Lookout weekly feed
 My blog, Technical Debt for Policymakers, offers
resources, insights, and conversations of interest to policymakers who are concerned with managing
technical debt within their organizations. Get the millstone of technical debt off the neck of your
organization!
My blog, Technical Debt for Policymakers, offers
resources, insights, and conversations of interest to policymakers who are concerned with managing
technical debt within their organizations. Get the millstone of technical debt off the neck of your
organization!