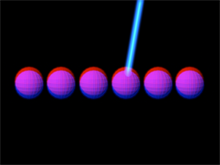
Six atoms in a Schrödinger "cat" state. A "cat" state in quantum mechanics is a state that can be interpreted as consisting of two or more states that classically conflict.
The term arises from a debate undertaken by Erwin Schrödinger and Albert Einstein. In the summer of 1935, in a startlingly brilliant example of constructive conflict, Schrödinger and Einstein exchanged a number of letters debating a point of the theory of quantum mechanics. The system in question, which was fictitious, consisted, in part, of a box containing a cat. They were able to devise a thought experiment in which it could be argued that the cat was both alive and dead. This issue is still undergoing debate.
In an experiment conducted at the U.S. National Institute of Standards and Technology, experimenters were able to induce six ions into a quantum "cat" state in which their nuclei are collectively each spinning both clockwise and counterclockwise. Photo courtesy U.S. National Institute of Standards and Technology.
Constructive conflict is creative. Groups engaged in constructive conflict can produce results that are often superior to what they could have achieved without conflict. But when conflict turns toxic, both results and relationships can suffer. Resolving toxic conflict can limit the damage it does, but some damage often remains. That's one reason why preventing toxic conflict is a strategy superior to effectively resolving that same conflict.
Here are some guidelines for preventing toxic conflicts from forming.
- Understand the Fundamental Attribution Error
- The Fundamental Attribution Error (FAE) is the human tendency to explain the behavior of others by attributing too much to character (and especially character flaws), and not enough to circumstances (and especially extenuating circumstances).
- Because of the FAE, we sometimes experience remarks as intentional attacks, when they are actually evidence that the person making the remark is misinformed. The FAE leads us to anger and frustration when we experience unpleasant consequences of others' behavior. Similarly, when the actions of others cause us difficulty, awareness of the Fundamental Attribution Error makes us less likely to experience irritation.
- Understand the online disinhibition effect
- The online disinhibition effect explains why toxic conflict erupts so easily in virtual environments. Briefly, because the virtual environment lacks ways of connecting individuals with the consequences of antisocial behavior, the virtual environment suppresses inhibitions that limit such behavior in the face-to-face context. See "Toxic Conflict in Virtual Teams: Dissociative Anonymity," Point Lookout for April 3, 2013, for more.
- Educate people about this phenomenon. When we know what can happen, when we have a shared understanding of the phenomenon, and when we have a name for it, we can deal with it better when it occurs. More important, we're less likely to fall into the difficulty.
- Choose communications media carefully
- In communications, In communications, the greater
the need for delicacy,
the more necessary are
immediacy and privacythe greater the need for delicacy, the more necessary are immediacy and privacy. Communications media vary widely in their degree of immediacy and in the privacy they afford. - For example, email is dangerous. Many toxic conflicts arise from the simple act of using email to sort out honest but passionate disagreements. This problem is so widespread that it has a name: "flame war". Telephone is somewhat better than email, but still dangerous. Choose communications media carefully.
- Be intentional about building trust
- Trust doesn't just happen. It must be built intentionally, and carefully maintained. Workgroups that try to collaborate, while investing too little in building and maintaining trust, are especially vulnerable to toxic conflict.
- Become a student of trust-building strategies. Because the effectiveness of such strategies is strongly culture-dependent, recognize that the answers for your organization might require some original thought. But to get you started, take a look at "Express Your Appreciation and Trust," Point Lookout for January 16, 2002, and "Creating Trust," Point Lookout for January 21, 2009. And remember, abandoning trust-eroding strategies can itself be a trust-building strategy. For example, reducing the incidence of split assignments can reduce trust erosion. See How to Spot a Troubled Project Before the Trouble Starts for more.
We continue this exploration next time, focusing on the adoption and enforcement of behavioral norms. ![]() First issue in this series
First issue in this series ![]() Next issue in this series
Next issue in this series ![]() Top
Top ![]() Next Issue
Next Issue
Are you fed up with tense, explosive meetings? Are you or a colleague the target of a bully? Destructive conflict can ruin organizations. But if we believe that all conflict is destructive, and that we can somehow eliminate conflict, or that conflict is an enemy of productivity, then we're in conflict with Conflict itself. Read 101 Tips for Managing Conflict to learn how to make peace with conflict and make it an organizational asset. Order Now!
Your comments are welcome
Would you like to see your comments posted here? rbrenaXXxGCwVgbgLZDuRner@ChacDjdMAATPdDNJnrSwoCanyon.comSend me your comments by email, or by Web form.About Point Lookout
 Thank you for reading this article. I hope you enjoyed it and
found it useful, and that you'll consider recommending it to a friend.
Thank you for reading this article. I hope you enjoyed it and
found it useful, and that you'll consider recommending it to a friend.
This article in its entirety was written by a human being. No machine intelligence was involved in any way.
Point Lookout is a free weekly email newsletter. Browse the archive of past issues. Subscribe for free.
Support Point Lookout by joining the Friends of Point Lookout, as an individual or as an organization.
Do you face a complex interpersonal situation? Send it in, anonymously if you like, and I'll give you my two cents.
Related articles
More articles on Conflict Management:
 The Focus of Conflict
The Focus of Conflict- For some teams conflict seems to focus around one particular team member. The conflict might manifest
itself as either organizational or interpersonal issues, or both, but whatever the problem seems to
be, the problem is never the problem.
 Patterns of Conflict Escalation: II
Patterns of Conflict Escalation: II- When simple workplace disagreements evolve into workplace warfare, they often do so following recognizable
patterns. If we can recognize the patterns early, we can intervene to prevent serious damage to relationships.
Here's Part II of a catalog of some of those patterns.
 Power Mobbing at Work
Power Mobbing at Work- Mobbing is a form of group bullying of an individual — the target. Power mobbing occurs when a
politically powerful person orchestrates the mobbing. It's a form of bullying that's especially harmful
to the target and the organization.
 Pre-Decision Discussions: Reasoning
Pre-Decision Discussions: Reasoning- When we meet to resolve issues related to upcoming decisions, we sometimes rely on reasoning to help
find solutions. Contributions to these discussions generally use mixtures of deductive, inductive, and
abductive reasoning. How do they differ, and what are their strengths and risks?
 Tuckman's Model and Joint Leadership Teams
Tuckman's Model and Joint Leadership Teams- Tuckman's model of the stages of group development, applied to Joint Leadership Teams, reveals characteristics
of these teams that signal performance levels less than we hope for. Knowing what to avoid when we designate
these teams is therefore useful.
See also Conflict Management for more related articles.
Forthcoming issues of Point Lookout
 Coming October 1: On the Risks of Obscuring Ignorance
Coming October 1: On the Risks of Obscuring Ignorance- A common dilemma in knowledge-based organizations: ask for an explanation, or "fake it" until you can somehow figure it out. The choice between admitting your own ignorance or obscuring it can be a difficult one. It has consequences for both the choice-maker and the organization. Available here and by RSS on October 1.
 And on October 8: Responding to Workplace Bullying
And on October 8: Responding to Workplace Bullying- Effective responses to bullying sometimes include "pushback tactics" that can deter perpetrators from further bullying. Because perpetrators use some of these same tactics, some people have difficulty employing them. But the need is real. Pushing back works. Available here and by RSS on October 8.
Coaching services
I offer email and telephone coaching at both corporate and individual rates. Contact Rick for details at rbrenaXXxGCwVgbgLZDuRner@ChacDjdMAATPdDNJnrSwoCanyon.com or (650) 787-6475, or toll-free in the continental US at (866) 378-5470.
Get the ebook!
Past issues of Point Lookout are available in six ebooks:
- Get 2001-2 in Geese Don't Land on Twigs (PDF, )
- Get 2003-4 in Why Dogs Wag (PDF, )
- Get 2005-6 in Loopy Things We Do (PDF, )
- Get 2007-8 in Things We Believe That Maybe Aren't So True (PDF, )
- Get 2009-10 in The Questions Not Asked (PDF, )
- Get all of the first twelve years (2001-2012) in The Collected Issues of Point Lookout (PDF, )
Are you a writer, editor or publisher on deadline? Are you looking for an article that will get people talking and get compliments flying your way? You can have 500-1000 words in your inbox in one hour. License any article from this Web site. More info
Follow Rick
Recommend this issue to a friend
Send an email message to a friend
rbrenaXXxGCwVgbgLZDuRner@ChacDjdMAATPdDNJnrSwoCanyon.comSend a message to Rick
![]() A Tip A Day feed
A Tip A Day feed
![]() Point Lookout weekly feed
Point Lookout weekly feed
 My blog, Technical Debt for Policymakers, offers
resources, insights, and conversations of interest to policymakers who are concerned with managing
technical debt within their organizations. Get the millstone of technical debt off the neck of your
organization!
My blog, Technical Debt for Policymakers, offers
resources, insights, and conversations of interest to policymakers who are concerned with managing
technical debt within their organizations. Get the millstone of technical debt off the neck of your
organization!